Understand the most critical web application risks and how to protect your business from the code up
Software security is no longer a concern limited
to technical teams. It has become a strategic business priority. In a scenario where cyberattacks are increasingly sophisticated
and frequent, vulnerabilities in applications represent more than technical issues: they pose real risks to reputation, operational
continuity, and customer trust.
This is where web application security takes center
stage. After all, a large portion of today’s digital interactions, from internal systems to e-commerce platforms and
financial services, happens through the Internet. Every line of code exposed online can become an entry point for threats
if not properly protected.
What is the OWASP Top 10 and why does it matter
To help companies and developers understand and
mitigate these risks, OWASP (Open Web Application Security Project) maintains the OWASP Top 10, one of the world’s most
important references in web application security.
It is a widely recognized guide that gathers the
ten most critical categories of vulnerabilities based on real-world data, expert analysis, and global consensus. More than
just a list, the OWASP Top 10 acts as a continuous warning about the key security concerns in software development.
Its value lies in its practicality: it translates
complex threats into understandable and actionable risks, enabling technical teams and business leaders to make smarter security
decisions from the very beginning of a project.
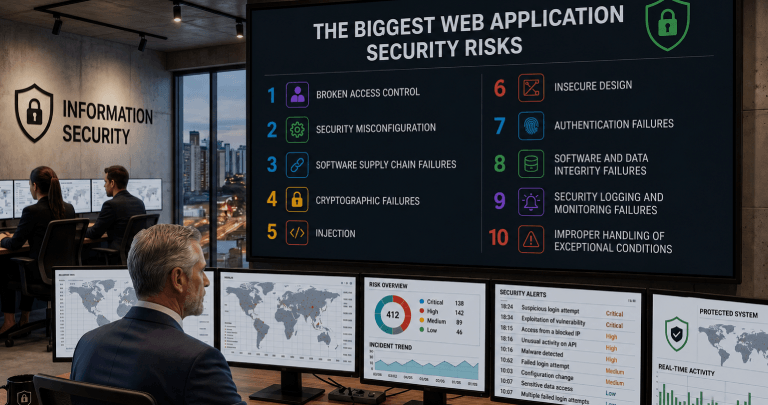
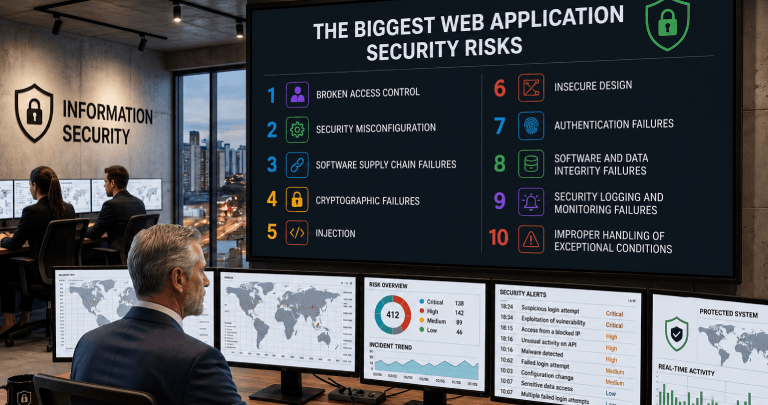
OWASP Top 10 2025: what’s in focus
This is the OWASP 2025 list:
1. Broken Access Control
2. Security Misconfiguration
3. Software Supply Chain Failures
4. Cryptographic Failures
5. Injection
6. Insecure Design
7. Authentication Failures
8. Software or Data Integrity Failures
9. Security Logging and Alerting Failures
10. Mishandling of Exceptional Conditions
Understanding each risk
1. Broken Access Control: occurs when users gain access
to data or functionalities without proper authorization, violating defined permissions.
2. Security Misconfiguration: happens when systems, servers,
or applications are configured incorrectly, leaving exploitable gaps.
3. Software Supply Chain Failures: involve vulnerabilities
introduced through compromised third-party libraries, dependencies, or components.
4. Cryptographic Failures: result from the incorrect
or insufficient use of encryption, exposing sensitive data to interception or leakage.
5. Injection: occurs when malicious input is interpreted
as commands by the system, enabling unauthorized data manipulation or code execution.
6. Insecure Design: refers to flaws in the application’s
architecture where security requirements are not considered from the start.
7. Authentication Failures: happens when login and identity
validation mechanisms are weak or poorly implemented.
8. Software or Data Integrity Failures: allow code or
data to be altered without detection, compromising system reliability.
9. Security Logging and Alerting Failures: occurs when
relevant events are not properly logged or monitored, making incident detection more difficult.
10. Mishandling of Exceptional Conditions: happens when
errors and exceptions are not handled correctly, potentially exposing sensitive information or opening security gaps.
What the list reveals
The latest version reinforces a clear trend: security
must evolve alongside modern architectures and the growing use of APIs, Cloud Computing, and Artificial Intelligence.
Among the most significant highlights is the persistence
of well-known risks such as access control failures, security misconfigurations, and injection-related vulnerabilities. However,
the current landscape amplifies the impact of these issues, especially in highly distributed and integrated environments.
Another relevant aspect is the increasing focus
on design and architectural flaws. This reflects a shift in mindset: fixing isolated errors is no longer enough, meaning security
must be considered from the system’s conception. In addition, the software supply chain remains a critical point, as
external dependencies can represent significant risks when not managed properly.
There is also growing concern around authentication
and identity management, particularly due to the rise in attacks exploiting compromised credentials and poorly implemented
authentication mechanisms.
Security trends that cannot be ignored
The OWASP Top 10 2025 makes one thing clear: security
is no longer an isolated phase in the development lifecycle. It must be continuous, integrated, and strategic.
One of the main trends is the strengthening of the
“security by design” concept, where security is built in from the start rather than added later. This reduces
costs, avoids rework, and significantly increases application robustness.
Another important trend is the adoption of DevSecOps
practices, which integrate security into the development and continuous delivery pipeline. Automating security testing and
embedding validations throughout the process becomes essential to keep pace with modern delivery speeds. Furthermore, the
growing complexity of systems (driven by microservices, APIs, and AI) requires a broader protection strategy that goes beyond
code and considers the entire digital ecosystem.
Security as a competitive advantage
Companies that treat security merely as an obligation
tend to react to problems. Those that see it as part of the value delivered to customers position themselves ahead of the
market. Ensuring data protection, system reliability, and operational integrity is not just a technical matter. It
is a competitive advantage that directly impacts customer trust and business sustainability.
Visionnaire: 30 years developing software with
security at its core
At Visionnaire, security has never been an afterthought.
Over 30 years as a Software Factory, we have built a strong culture where protection is an essential part of the entire development
process.
Today, as an AI Factory, this commitment becomes
even more relevant. We work with advanced technologies, sensitive data, and critical systems, demanding an even higher level
of security rigor.
Our approach integrates best practices from conception
to delivery, aligning development, architecture, and operations with the latest cybersecurity principles. This means reducing
vulnerabilities, anticipating risks, and ensuring every solution is robust, reliable, and prepared for the challenges of the
digital world.
If security is a priority for your business, it
also needs to be a priority in your software development process. Contact us
and discover how Visionnaire can help your business.




